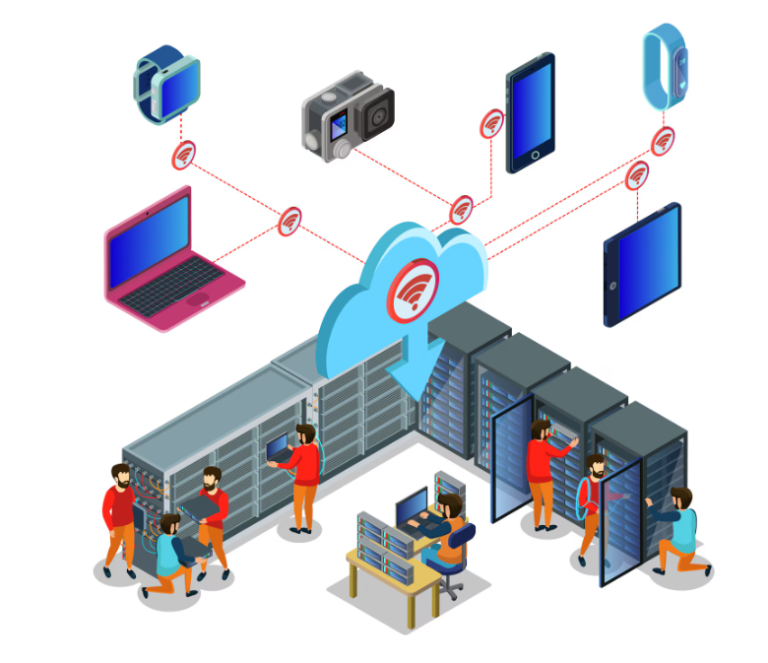
Every digital organization depends on one critical foundation its network. From internal servers and employee workstations to cloud connectors and IoT devices, the network is what binds an enterprise together. But it’s also what cyber attackers target first.
To protect this foundation, businesses turn to Network Penetration Testing, supported by comprehensive Penetration Testing Services. These assessments identify exploitable weaknesses, validate defense mechanisms, and empower organizations to fortify every connection point before attacker’s strike.
What Is Network Penetration Testing?
Network Penetration Testing is a controlled, simulated cyberattack performed by ethical hackers to assess the security of an organization’s IT infrastructure. The objective is to find vulnerabilities in systems, devices, and configurations that could allow unauthorized access or data breaches.
This testing involves both external and internal assessments:
- External Network Penetration Testing focuses on internet-facing assets such as firewalls, VPN gateways, and web servers.
- Internal Network Penetration Testing simulates attacks from within the corporate network, assessing insider threats, compromised devices, and misconfigurations.
The result is a 360-degree understanding of your network’s resilience against real-world threats.
Why Network Testing Is Essential
Cybercriminals often exploit the simplest vulnerabilities an open port, an outdated firmware, or weak authentication settings. Without proactive network testing, such weaknesses remain hidden until it’s too late.
Key Benefits of Network Penetration Testing
- Early Threat Identification: Detect exploitable vulnerabilities before attackers do.
- Compliance Readiness: Meet ISO 27001, SOC 2, HIPAA, and GDPR security mandates.
- Business Continuity: Prevent operational downtime caused by ransomware or intrusion.
- Data Protection: Ensure customer and corporate information remains confidential.
- Risk Prioritization: Focus remediation efforts on the most critical vulnerabilities.
By regularly performing network tests, organizations gain assurance that their defenses are effective, current, and compliant.
The Process of Network Penetration Testing
Professional Penetration Testing Services follow a structured methodology that aligns with international standards like PTES, OWASP, and NIST.
- Planning and Scoping
The engagement begins with defining the scope whether testing internal networks, external systems, or both. The testing team establishes goals, permissions, and safety measures to ensure legal and operational compliance.
- Reconnaissance
Ethical hackers gather information about the target environment domains, IP ranges, open ports, and network services through passive and active reconnaissance.
- Vulnerability Discovery
Automated tools and manual verification identify configuration weaknesses, outdated software, and exploitable entry points.
- Exploitation
Controlled attacks simulate real-world intrusions to test whether vulnerabilities can be exploited to gain unauthorized access, escalate privileges, or exfiltrate data.
- Post-Exploitation Analysis
This step assesses the potential impact how much data could be compromised, how lateral movement might occur, and whether existing defenses can detect and stop the attack.
- Reporting and Remediation
A comprehensive report outlines findings, their severity, and specific remediation steps. This includes an executive summary for leadership and technical details for IT teams.
- Retesting and Validation
Once fixes are applied, retesting confirms that all vulnerabilities have been effectively resolved.
This full lifecycle ensures that your organization not only identifies weaknesses but also verifies that they are closed for good.

Common Vulnerabilities Found in Network Testing
Even the most advanced organizations can have overlooked flaws. Network Penetration Testing often uncovers issues such as:
- Unpatched operating systems or software.
- Misconfigured firewalls or routers.
- Weak or default passwords.
- Insecure VPN configurations.
- Outdated SSL/TLS encryption protocols.
- Open or unnecessary network ports.
- Poor segmentation between critical and non-critical systems.
These issues may appear minor, but attackers exploit them to pivot across networks and access sensitive data.
How Professional Penetration Testing Services Add Value
Choosing the right testing partner determines the quality and impact of your assessment. Aardwolf Security’s Penetration Testing Services are designed not only to identify vulnerabilities but to strengthen overall resilience through expert analysis and clear communication.
Key Differentiators of Aardwolf Security
- Certified Experts: OSCP, CREST, and CEH-certified testers with deep technical and business insight.
- Manual + Automated Approach: Combining intelligent scanning tools with hands-on exploitation for maximum accuracy.
- Custom Engagements: Tailored testing strategies for networks, web apps, APIs, and cloud environments.
- Compliance-Ready Reports: Documentation aligned with ISO, SOC 2, and PCI DSS standards.
- Actionable Guidance: Detailed remediation advice with business impact prioritization.
- Revalidation Support: Optional retesting to confirm closure of vulnerabilities.
Aardwolf Security transforms penetration testing from a compliance task into a proactive risk management program.
Integrating Testing into a Continuous Security Strategy
Modern threats evolve daily, so one-time testing isn’t enough. To maintain long-term security, Aardwolf recommends a continuous testing model:
- Quarterly or Biannual Network Pen Tests depending on infrastructure size.
- Testing After Major Changes such as software upgrades or cloud migrations.
- Continuous Monitoring Tools for real-time visibility between assessments.
- Training and Awareness to reduce human errors leading to breaches.
By integrating Penetration Testing Services into your broader security strategy, your organization stays resilient even as technologies and threats evolve.
The Business Impact
Investing in Network Penetration Testing provides measurable business outcomes:
- Reduced Incident Response Costs: Early detection prevents expensive recovery efforts.
- Improved Customer Trust: Demonstrates a strong commitment to data protection.
- Operational Efficiency: Insights streamline patch management and security workflows.
- Board-Level Assurance: Quantifiable risk reduction supports strategic decision-making.
When performed by experts like Aardwolf Security, these benefits extend beyond compliance they strengthen brand reputation and long-term growth.
Conclusion
In today’s hyper-connected world, your network is your greatest asset and your greatest vulnerability. Network Penetration Testing, powered by expert Penetration Testing Services, provides the visibility and confidence to defend your enterprise from modern cyber threats.
Aardwolf Security’s proven methodology, certified professionals, and tailored guidance ensure that every test delivers actionable results. With continuous evaluation, transparent reporting, and hands-on support, your organization can stay secure, compliant, and prepared for whatever comes next.
Cybersecurity isn’t a one-time effort it’s an ongoing partnership. With Aardwolf Security, your network becomes more than resilient it becomes impenetrable.